In February 2017, I co-authored a blog detailing our build of an 8-GPU password cracker. Over the past 8 years, it’s had millions of views and thousands of comments. To all the concerned writers,...


In February 2017, I co-authored a blog detailing our build of an 8-GPU password cracker. Over the past 8 years, it’s had millions of views and thousands of comments. To all the concerned writers,...

Whether doing security research or troubleshooting networks, network sniffers and packet analysis can be invaluable tools. If you're a network engineer like me, you've probably been holding onto...

In penetration testing, it’s important to have an accurate scope and even more important to stick to it. This can be simple when the scope is limited to a company’s internet service provider (ISP)...

What is a Pwnagotchi? From the Website: Pwnagotchi is an A2C-based “AI” powered by bettercap and running on a Raspberry Pi Zero W that learns from its surrounding WiFi environment in order to...

Insert under image - Palo Alto Networks firewalls have the ability to create security policies and generate logs based on users and groups, and not just IP addresses. This functionality is called...
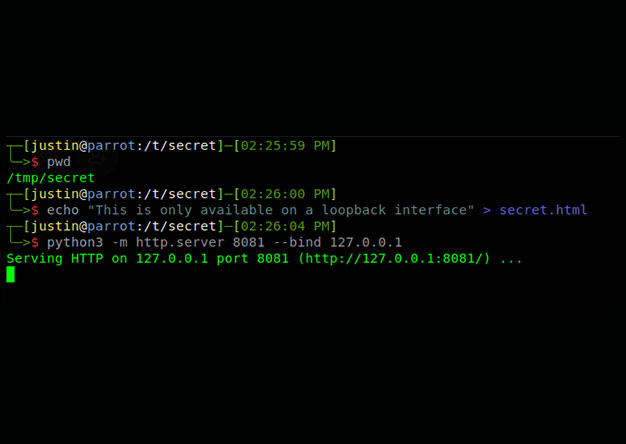
One of the greatest yet unknown dangers that face any cloud-based application is the combination of an SSRF vulnerability and the AWS Metadata endpoint. As this write up from Brian Krebbs explains,...
Background While experts have agreed for decades that passwords are a weak method of authentication, their convenience and low cost has kept them around. Until we stop using passwords or start using...

Why? … Stop asking questions! Background In February 2017, we took our first shot at upgrading our old open-frame 6 GPU cracker (NVIDIA 970). It served us well, but we needed to crack 8 and...
At SynerComm's Fall IT Summit 2018 we presented a talk about the top 5 attacks used to compromise a Domain Administrator account. As a short recap, the top five are the following: 1.Permissive...
On August 15th, 2018 a vulnerability was posted on the OSS-Security list. This post explained that OpenSSH (all versions prior to and including 7.7) is vulnerable to username enumeration by sending...